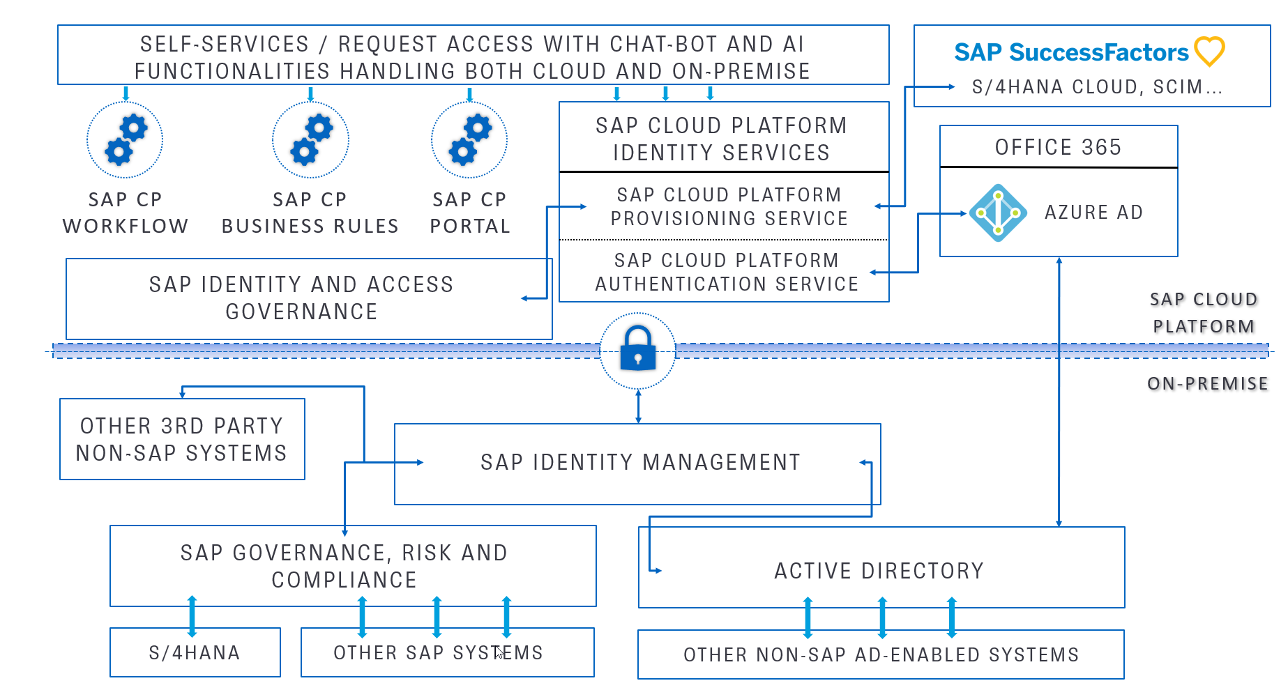
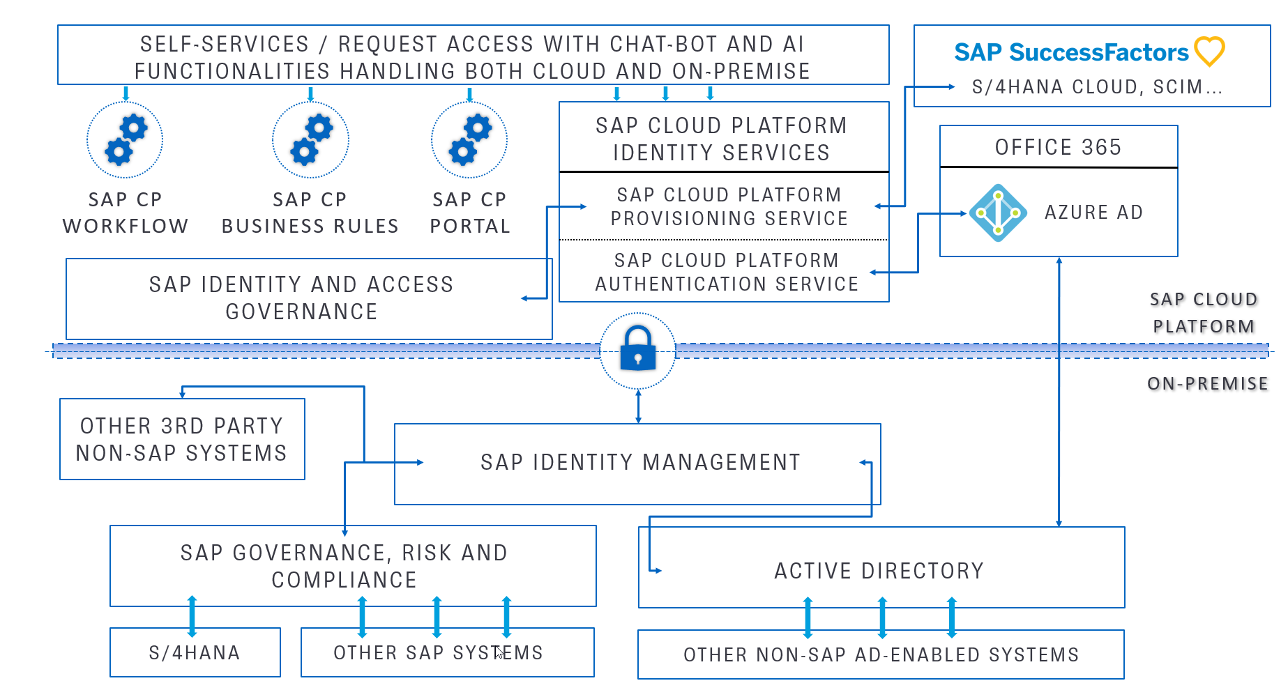
Hybrid landscape can cover most of the enterprises nowadays since they are at a stage where they have not yet moved completely to the cloud, their on-premise landscape is still more important, but innovation and pace of changes have already pushed them in the direction of the cloud.
The on-premise world consists of numerous ABAP systems, which include S/4HANA, GRC and others. GRC is connected to all SAP ABAP systems and to IDM for business role synchronization and provisioning. Additionally, IDM is used to connect to Active Directory, which is the bridge to multiple other applications, which rely on AD for authentication and authorization. Other 3rd party non-SAP systems are also connected and provisioned from IDM.
On the cloud side, IDM is connected to IPS, which has a number of proxy systems maintained to cloud solutions like SAP SuccessFactors, S/4HANA Cloud and other SCIM enabled ones. The enterprise is using Microsoft Office 365, which is connected to the backend Active Directory through a replication to Azure AD, which is also connected to IAS as a cloud identity provider, making sure that all employees have access to enterprise applications using one and the same credentials.
IAG is also present in the cloud and connected to the on-premise GRC for a richer set of functionalities. It actively uses three other services on the SAP Cloud Platform - the Workflow Service - for handling the approval workflows, the Business Rules Service - for controlling automated decisions using Excel-like tables and the Provisioning Service – for connecting to the cloud target systems. The access to these is facilitated using the Portal service. We complete the picture with a unified custom self-service layer running in the cloud, which offers an intuitive SAP Fiori interface integrated with chatbot functionality. Based on AI algorithms, the interface can correctly categorize the request and send it to the proper workflows/systems for processing, thus hiding the underlying complexity from the end user, whose sole purpose is to receive the requested access as soon as possible and as transparently as possible.
Do not consider this landscape as a project created in one go. This is a holistic strategy to make the company future-proof. So, splitting it into multiple small steps, which are successfully completed one after the other will provide better sense of where you are going and if you need to adapt the course along the way.